In continuation of my previous post , in this post i will be covering tenant side configuration of vCloud Director 10 along with NSX-T.
Create OrgVDC
To provide resources to an Tenant organization, you create one or more organization virtual data centers for tenant organization.To Create an OrgVDC , you need to go to “Cloud Resources” then “Organization VDCs” and Click on New:
- Name Tenant OrgVDC appropriately
- Select the Organisation
- Select the PVDC which is NSX-T backed.
- Choose appropriate allocation model (flex)
- Configure reservation pool related settings
- Choose appropriate storage policy
- enable “Network Pool” and select correct network pool and specify max networks
- Review and click on Finish.
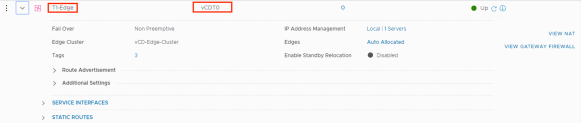
Create Org Edges
To connect tenants networks created inside org vDC to out side , we need to create edge gateways, which internally automatically create T1 router, here are the steps to create edge:
- Login to tenant by clicking on “Open in Tenant Portal” and go to Edges & click New
- Name Tenant edge appropriately
- Select IP segment and reserve few IPs to talk to external world.
- Review configuration and submit
If you look back in to NSX-T , this will create a Tier-1 router automatically and connect it to Tier-0 router.
Org Edge supported Tenant Operation:
Currently the following T1 GW networking services are available to tenants:
- Firewall
- NAT
- DHCP (without binding and relay)
- DNS forwarding
- IPSec VPN with API only and only apply Policy based with pre share key.

Create Org Networks
The first network to create for tenant is an organization Virtual Datacenter network, An orgVDC network allows virtual machines in the orgVDC to communicate with each other and to access other networks, including orgVDC networks and external networks, either directly or through an Edge Gateway (T0) that can provide firewall and NAT services as of now. There are three type of org Networks:
Isolated:
You can add an isolated orgVDC network, which is accessible only by this organization. This network provides no connectivity to virtual machines outside this organization. Virtual machines outside of this organization have no connectivity to the virtual machines in the organization.
Routed:
Routed network control the access to an external network, System administrators and organization administrators can configure network address translation (NAT), firewall, and VPN settings to make specific virtual machines accessible from the external network.
Imported:
You can import existing NSX-T overlay switch in to org , for this networking type all networking need to be configured and managed out side of vCloud Director.
Tenant VM External Access:
As i said tenant networks are not advertised , we need to create SNAT rules to allow external access:


NOTE – Tenant can only self service Isolated and routed networks, there are few options like DFW and Load Balancer still has not been exposed to tenants.






