In continuation to my last two posts on using Terraform to automate various Cloud Director options, here is another one…In this post we are going to onboard a tenant using vCloud Director Terraform provider , (last post i did 5 steps) there are 12 steps that we are going to automate.Special thanks to my terraform for vCD Product Team who helped me in some of this stuff.
Here is my old posts on similar topic.

- Create a new External Network
- Create a new Organization for the Tenant
- Create a new Organization Administrator for this Tenant
- Create a new Organization VDC for the Tenant
- Deploy a new Edge gateway for the Tenant
- Create a new Routed Network for the Tenant
- Create a new Isolated Network for the Tenant
- Create a new Direct Network for the Tenant
- Create Organization Catalog
- Upload OVA/ISO to Catalog
- Creating vApp
- Create a VM inside vAPP
Step-1: Code for Creating External Network
As you know External Network is a Tenant connection to the outside world, By adding an external network, you register vSphere network resources for vCloud Director to use. You can create organization VDC networks that connect to an external network. few important parameters to consider:
- Resource Type – “vcd_external_network”
- vsphere_network – This is Required parameter you need to provide a DV_PORTGROUP or Standard port group names that back this external network. Each referenced DV_PORTGROUP or NETWORK must exist on a vCenter server which is registered with vCloud Director.
- Type –
- For dv Port Group , use Type – DV_PORTGROUP
- For Standard Port Group , use Type – NETWORK
- retain_net_info_across_deployments – (Optional) Specifies whether the network resources such as IP/MAC of router will be retained across deployments. Default is false.
#Create a new External Network for "tfcloud"
resource "vcd_external_network" "extnet-tfcloud" {
name = "extnet-tfcloud"
description = "external network"
vsphere_network {
vcenter = "vcsa.dp-pod.zpod.io" #VC name registered in vCD
name = "VM Network"
type = "NETWORK"
}
ip_scope {
gateway = "10.120.30.1"
netmask = "255.255.255.0"
dns1 = "10.120.30.2"
dns2 = "8.8.4.4"
dns_suffix = "tfcloud.org"
static_ip_pool {
start_address = "10.120.30.3"
end_address = "10.120.30.253"
}
}
retain_net_info_across_deployments = "false"
}
Step-2: Code for New Organization
In this section , we are going to create a new organization named “tfcloud” which is enabled to use, This section creates a new vCloud Organisation by specifying the name, full name, description, VM Quota , vApp lease etc… Quota, lease etc..Cloud Provider must need to enter based on the commitment with tenant organization.
#Create a new org name "tfcloud"
resource "vcd_org" "tfcloud" {
name = "terraform_cloud"
full_name = "Org created by Terraform"
is_enabled = "true"
stored_vm_quota = 50
deployed_vm_quota = 50
delete_force = "true"
delete_recursive = "true"
vapp_lease {
maximum_runtime_lease_in_sec = 0
power_off_on_runtime_lease_expiration = false
maximum_storage_lease_in_sec = 0
delete_on_storage_lease_expiration = false
}
vapp_template_lease {
maximum_storage_lease_in_sec = 0
delete_on_storage_lease_expiration = false
}
}
Step-3: Code for Creating Organisation Administrator
Once as a provider you created Org, this org need an admin, below code will create local org admin. In this code everything is self explanatory but few important parameters explained here:
- Resource Type – “vcd_org_user”
- org & name – these are variable, referred in variable file.
- role – role assigned to this user
- password – initial password assigned
#Create a new Organization Admin
resource "vcd_org_user" "tfcloud-admin" {
org = vcd_org.tfcloud.name
name = "tfcloud-admin"
password = "*********"
role = "Organization Administrator"
enabled = true
take_ownership = true
provider_type = "INTEGRATED" #INTEGRATED, SAML, OAUTH stored_vm_quota = 50 deployed_vm_quota = 50 }
Step-4: Code for Creating new Organization VDC
So till now we created External Network, Organization and Organization administrator , next is to create a organization virtual data center , so that tenant can provision VMs, Containers and Applications. few important configuration parameters to consider:
- name – vdc-tfcloud
- Resource Type – “vcd_org_vdc”
- Org – referring org name created in previous step
- Allocation Pool – Pay as you go (represented as “AllocationVApp”).
- network_pool_name – Network pool name as defined during provider config.
- provider_vdc_name – Name of Provider VDC name.
- Compute & Storage – Define compute and storage allocation.
- network_quota – Maximum no. of networks can be provisioned in to this VDC
# Create Org VDC for above org
resource "vcd_org_vdc" "vdc-tfcloud" {
name = "vdc-tfcloud"
org = vcd_org.tfcloud.name
allocation_model = "AllocationVApp"
provider_vdc_name = "vCD-A-pVDC-01"
network_pool_name = "vCD-VXLAN-Network-Pool"
network_quota = 50
compute_capacity {
cpu {
limit = 0
}
memory {
limit = 0
}
}
storage_profile {
name = "*"
enabled = true
limit = 0
default = true
}
enabled = true
enable_thin_provisioning = true
enable_fast_provisioning = true
delete_force = true
delete_recursive = true
}
Step-5: Code for Creating Edge Gateway for Tenant
This next section creates a new vCloud Organization Edge Gateway by specifying the name, full name, and description. Provider configures an edge gateway to provide connectivity to one or more external networks.
- Resource Type – “vcd_edgegateway”
- Configuration – compact
- Advanced – this will be an advance edge
- distributed_routing – distributed routing is enabled
- external_network – uplink information towards DC exit.
# Create Org VDC Edge for above org VDC
resource "vcd_edgegateway" "gw-tfcloud" {
org = vcd_org.tfcloud.name
vdc = vcd_org_vdc.vdc-tfcloud.name
name = "gw-tfcloud"
description = "tfcloud edge gateway"
configuration = "compact"
advanced = true
external_network {
name = vcd_external_network.extnet-tfcloud.name
subnet {
ip_address = "10.120.30.11"
gateway = "10.120.30.1"
netmask = "255.255.255.0"
use_for_default_route = true
}
}
}
Step-6: Code for Creating Organization Routed Network
An organization VDC network with a routed connection provides controlled access to machines and networks outside of the organization VDC. System administrators (Providers) and organization administrators can configure network address translation (NAT) and firewall settings on the network’s Edge Gateway to make specific virtual machines in the VDC accessible from an external network. Things to consider:
- resource -> must be of type “vcd_network_routed”
- Define other networking information
# Create Routed Network for this org
resource "vcd_network_routed" "net-tfcloud-r" {
name = "net-tfcloud-r"
org = vcd_org.tfcloud.name
vdc = vcd_org_vdc.vdc-tfcloud.name
edge_gateway = vcd_edgegateway.gw-tfcloud.name
gateway = "192.168.200.1"
static_ip_pool {
start_address = "192.168.200.2"
end_address = "192.168.200.100"
}
}
Step-7: Code for Creating Org Isolated Network
An isolated organization VDC network provides a private network to which virtual machines in the organization VDC can connect. This network provides no connectivity to machines outside this organization VDC. Things to consider:
- resource -> must be of type “vcd_network_isolated”
- Define other networking information like ips etc
# Create Isolated Network for this org
resource "vcd_network_isolated" "net-tfcloud-i" {
name = "net-tfcloud-i"
org = vcd_org.tfcloud.name
vdc = vcd_org_vdc.vdc-tfcloud.name
gateway = "192.168.201.1"
static_ip_pool {
start_address = "192.168.201.2"
end_address = "192.168.201.100"
}
}
Step-8: Code for Creating Organisation Direct Network
This is restricted to System Administrator of vCloud Director Cloud Providers, A System Administrator can create an organization virtual datacenter network that connects directly to an IPv4 or IPv6 external network. VMs on the organization can use the external network to connect to other networks, including the Internet. Things to consider:
- resource -> must be of type “vcd_network_direct”
- Define other networking information
- In this we are connecting directly to external network which created in step-1
# Create Direct Network for this org
resource "vcd_network_direct" "net-tfcloud-d" {
name = "net-tfcloud-d"
org = vcd_org.tfcloud.name
vdc = vcd_org_vdc.vdc-tfcloud.name
external_network = "extnet-tfcloud"
}
Step-9: Code for Creating Organization Catalog
Catalog allow Tenant to group vApps and media files , in this step provider is providing a private catalog to tenant,Things to consider:
- resource -> must be of type “vcd_catalog”
- Define catalog related information information
# Create Default catalog for this org
resource "vcd_catalog" "cat-tfcloud" {
org = vcd_org.tfcloud.name
name = "cat-tfcloud"
description = "tfcloud catalog"
delete_force = "true"
delete_recursive = "true"
depends_on = [vcd_org_vdc.vdc-tfcloud]
}
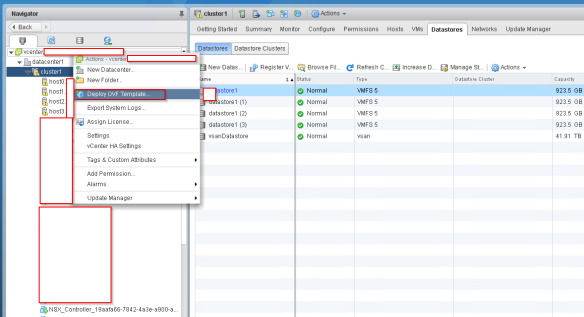
Step-10: Code for Uploading OVA in to Catalog
It’s up to provider, they can upload few catalog items like .iso and .ova for tenants to consume in to above private catalog or can share with them public catalog, in this case we are uploading few items in to this private catalog.Things to consider:
- resource -> must be of type “vcd_catalog_item”
- ova_path -> it will be a path of your local directory to upload image.
- Define catalog related information information
# Create Default catalog for this org
resource "vcd_catalog_item" "photon-hw11" {
org = vcd_org.tfcloud.name
catalog = vcd_catalog.cat-tfcloud.name
name = "photon-hw11"
description = "photon-hw11"
ova_path = "/Users/tripathiavni/desktop/Sizing/photon-hw11-3.0-26156e2.ova"
upload_piece_size = 5
show_upload_progress = "true"
}
Step-11: Code for Creating vAPP
In this step as a provider we are creating a vAPP which will hold few client binaries to run Container Service Extension. while creating vAPP things to consider:
- resource -> must be of type “vcd_vapp”
- ova_path -> it will be a path of your local directory to upload image.
- Define catalog related information information
# Create vApp for this org
resource "vcd_vapp" "CSEClientVapp" {
name = "CSEClientVapp"
org = vcd_org.tfcloud.name
vdc = vcd_org_vdc.vdc-tfcloud.name
# This dependency is must to avoid a lock during destroy
depends_on = [vcd_network_routed.net-tfcloud-r]
}
Step-12: Code for Creating Virtual Machine
In above vAPP , we will add a VM which is running Photon OS, while creating VM, Things to consider:
- resource -> must be of type “vcd_vapp_vm”
- catalog_name -> Catalog that we created in above step.
- Define other VM related information.
# Create Default catalog for this org
resource "vcd_vapp_vm" "CSEClientVM" {
name = "CSEClientVM"
org = vcd_org.tfcloud.name
vdc = vcd_org_vdc.vdc-tfcloud.name
vapp_name = vcd_vapp.CSEClientVapp.name
catalog_name = vcd_catalog.cat-tfcloud.name
template_name = vcd_catalog_item.photon-hw11.name
cpus = 2
memory = 1024
network {
name = vcd_network_routed.net-tfcloud-r.name
type = "org"
ip_allocation_mode = "POOL"
}
}
Putting it all together:
So i have put all this code in to a single file and also created a variable file, which will allow providers to on-board a new Tenant less then “5 minute” , provider admin just need to update few parameters in to the variable file like:
- vcd_user -> Cloud Admin user name
- vcd_pass -> Cloud Admin password
- vcd_url -> Cloud Director provider URL

Once you input the parameters, run terraform plan and Apply the plan, this entire process should not take more than 10 minutes to complete.
- Terraform Plan -out m4.tfplan
As you can see in above images terraform plan will add “12” items in to my Cloud Director.
- Terraform apply “m4.tfplan”
Finally terraform created all the 12 resources that we expected it to create.
Result:
As described above all 12 tasks related to a Tenant on-boarding got successfully completed and if you notice highlighted boxes , everything is over in less than around 8 minutes including uploading an OVA isn’t it awesome ?
NOTE: There isn’t need to define org/vdc in every resource if it is defined in provider unless you working with a few org/VDCs.
Here i am attaching variable and code file , which you can use it in your environment by just changing variable file contents which i explained above. pls try these files in to a non-prod environment and make your self comfortable before doing it in production. here is the full content of above to Download Please share feedback , suggestion any in the comment section…